
Cybersecurity Awareness Episode 4: Phishing and Ransomware - We’re bringing you another free security awareness video!
Enjoy the newest video! Please share on social channels so others working at home at this unprecedented time can get a little levity in our day and also be better educated on how to protect ourselves.
Phishing, we’ve heard of it, but what does it mean? In summary, it is a tool and method attackers use to try and coerce people into clicking on a malicious site or download, potentially leading to a security issue.
On the dark web, phishing is a very popular and effective way to try to steal data, lock data, delete data, gain access, or take over a computer. Phishing usually comes through email but can come via text message or other collaboration apps like Slack, Skype, or GroupMe.
Here are some signs of a phishing attempt. While the diagram below is email based, the same principles can be applied to the other communication methods mentioned above:
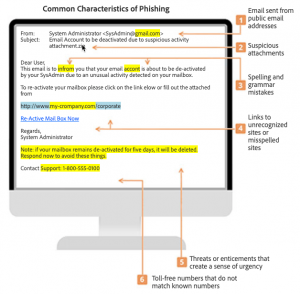
Phishing is usually obvious, and the above signs show prominently. However, some phishing attempts are tricky and it’s hard to spot a legitimate message from an illegitimate one. For example, amid the current crisis, many phishing attempts are using COVID-19 as their hook. Also, we’ll all recall, shortly after GDPR was passed there was a flurry of companies sending out updates to their privacy policy and emailing people about it. Well, attackers took advantage of this world-wide explosion of privacy policy updates and tricked many into clicking the links to “view or accept the new privacy policy”.
One of the best methods for protecting organizations and individuals against phishing is to report phishing attempts (Outlook > Report Phishing, Gmail > Report Spam). This helps the tool get smarter so that others don’t potentially get the same or similar emails.
As you’ll see on display in this newest security awareness video, ransomware is an especially dangerous consequence of falling for a phishing attempt. Ransomware is software that locks down data by encrypting it and won’t be unlocked through decryption until a ransom is paid. To protect yourself from ransomware:
- First, be wary of suspicious emails and look for the signs.
- Second, make sure your security software is up to date and running. It’ll help stop the ransomware in its tracks.
- Third, if ransomware is installed, then if you’ve backed up your data, you can ignore the threat and restore the data. Unfortunately, in many cases and especially for large enterprises, the cost of the ransom is significantly less than the cost to restore the data, even if it’s backed up. Therefore, the first and second layers of protection are critical.
These videos are brought to you by Adobe, National Cyber Security Alliance, and Speechless Inc.
More from this series:
Cybersecurity Awareness Episode 1: Passwords
Cybersecurity Awareness Episode 2: Data Handling
Cybersecurity Awareness Episode 3: Computer Theft
Cybersecurity Awareness Episode 4: Phishing and Ransomware
Cybersecurity Awareness Episode 5: Removable Media
Cybersecurity Awareness Episode 6: Vishing
Cybersecurity Awareness Episode 7: Internet Downloads
Cybersecurity Awareness Episode 8: Wi-Fi
Darryl Cresswell
CEO & President
MYDWARE IT Solutions Inc.




