Exposing 10 Steps You Need to ACTUALLY Build A Cyber-Smart Team
Build a Cyber-Smart Team With Our Free Checklist
Take Your FREE Checklist NOW!
The Business Continuity Plan To Get Ahead Of 97.2% Of Your Competitors
Learn the strategies top businesses use to turn disruptions into opportunities and stay ahead.
Take Your FREE Checklist NOW!

Transform Your Organization With Smart Technology
Time To Grow Your Business Faster And Smarter!
Get a free copy of the checklist now!

Hackers Are Now Powerful Than Ever... Are You?
Time To Beat These Cybercriminals Using These 4 AI Solutions For Your Business’ Security
Get a free copy of the checklist now!

Is your company ready for a security breach? Find out using our free checklist!
Assess your cybersecurity preparedness and identify areas for improvement.
Get a free copy of the checklist now!
BEYOND THE BREACH: How Effective is your Incident Response Plan?
Evaluate your readiness in cybersecurity and uncover avenues for enhancement.
Get a free copy of the checklist now!

Boost Your Business by Taking Proactive Measures to Safeguard Data
Data breaches are escalating, and businesses such as yours are in the crosshairs. Lacking a strong defense leaves your enterprise vulnerable to cyberattacks, which can cause severe financial and reputational harm.
Get a free copy of the checklist now!
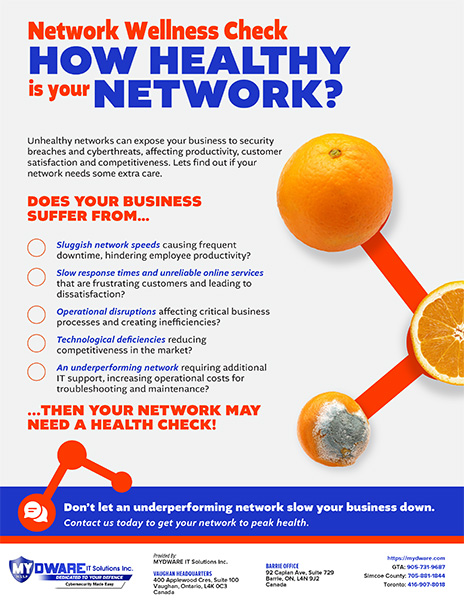
Network Wellness Check HOW HEALTHY is your NETWORK?
Unhealthy networks can slow your business down, making it vulnerable to cyberthreats and data breaches. Unfortunately, many business owners don’t know how to read the signs that indicate their network is in bad health.
Get a free copy of the checklist now!
The Essential Cyber Insurance Buyers Checklist For Businesses
Cyberattacks relentlessly target businesses, posing significant financial and reputational risks. It’s time to shield your business by securing the right cyber liability insurance.
Get a free copy of the checklist now!
The 4 Stages Of Cyber Risk Management
Cyberthreats are ever-present, lurking in the dark to exploit any vulnerability in your business tech. So, how do you secure your business from something that you can't see and know nothing about?
Get a free copy of the checklist now!
Achieve Digital Transformation With Our Checklist
If you’re confused about how to start your digital transformation journey, worry not. We have just the solution for you.
Get a free copy of the checklist now!
Can Your Security Culture Keep Cybercriminals at Bay?
Download our checklist to build a resilient cybersecurity culture in your organization.
Get a free copy of the checklist now!

Don’t Wait for an IT Disaster — Learn the Warning Signs Now
Is your technology holding you back from reaching your business goals? It’s time to identify potential roadblocks.
Get a free copy of the checklist now!
How to Make AI Work for Your Business
Artificial Intelligence (AI) can bring a lot of value to your company if implemented correctly. That's why AI execution should be a carefully thought-out process. Otherwise, it may turn out to be a costly headache.
Get a free copy of the checklist now!
Zero Trust Security
How to Make it Harder for Hackers to Do Their Job – Right Now
Are you concerned about the increasing sophistication and frequency of cyberattacks? Are you looking for an effective way to protect your business from cyberthreats? Moving toward a zero-trust cybersecurity model can help address your business’s security challenges. The question is, where do you begin?
Get a free copy of the checklist now!
How To Choose The Best Co-managed IT Partner For Your Business
Find the Right IT Partner to Drive Your Business Forward
As your business grows, managing your IT infrastructure becomes more challenging. Keeping up with cyberthreats and ensuring systems are secure can overwhelm your internal IT staff. Ensure your IT team gets the support they need by partnering with the right IT partner.
Get a free copy of the checklist now!

Manage Supply Chain Risks With These Strategies
Protect your business from supply chain attacks
Cybercriminals are constantly looking for the simplest way to harm multiple businesses. Supply chain attacks use flaws in the supply chain to infiltrate and damage systems or pull down the entire network. The frightening part is that while your vendors can expose you to these attacks, you can also expose them.
Get a free copy of the checklist now!
Don’t Let End-of-Service Technology Take Your Business Down
Don't Be Left in the Dark: Upgrade to a Supported Technology
While it may be tempting to continue using technology that has reached the end of its service until it is no longer functional, this can pose risks to your business. End-of-Service technology does not receive critical patches and updates, making it easier for threat actors to exploit.
Get a free copy of the checklist now!
The Secret to Responding Effectively to Cyber Incidents
Don’t ignore incident response best practices
Did you know that cyber incidents have increased by about 63% compared to last year? If you think your business is too small to be targeted by cybercriminals, you are leaving your business at risk.
Get a free copy of the checklist now!
Don't Let a Cyberattack Ruin Your Business
Get the Coverage You Need With Cyber Insurance
In today's highly digital era, businesses of all sizes are under constant attack from cybercriminals. Small businesses are easy targets since they lack enterprise-level security. Although the right security solutions can counter the rising threats, cyber incidents can still occur.
Get a free copy of the checklist now!




